“Can I use Power Automate for daily checks of SharePoint group members, to see if users added somebody who shouldn’t be there?”
Even though SharePoint groups should be a thing of the past, many users still use them. Instead of using an AD group with managed access they add users directly to SP groups. Which can be a problem – there might be users who have access to data without you even knowing.
That’s not an ideal situation, yet there’s always a flow to help you!
Get the group members
Since there’s no dedicated action, you’ll need another HTTP request to SharePoint. Similarly as when adding users to a SP group, you must find the group first. But don’t stop after the group name, you want to take it one step further – to the users in that group.
Method: GET
Uri:
_api/web/siteGroups/getByName('<groupName>')/Users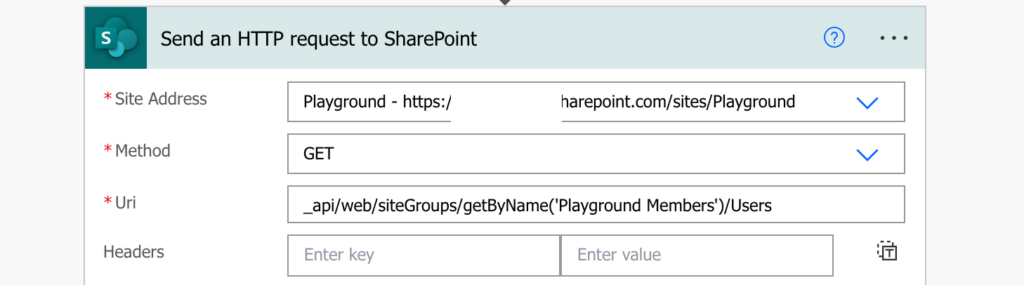
Such request will return list of all members of the group – AD groups and members alike. Since AD groups are fine and you’re interested only in the users, filter them out.
Navigate in the JSON to get an array with the users to use it in the ‘Filter array’ action.
body('Send_an_HTTP_request_to_SharePoint')?['d']?['results']While checking the JSON, you might also notice that there’s a difference between AD groups and users – users have a value in the ‘UserId’ parameter. Use it in the filter to remove all groups (where the ‘UserId’ is null).
item()?['UserId'] <is not equal to> null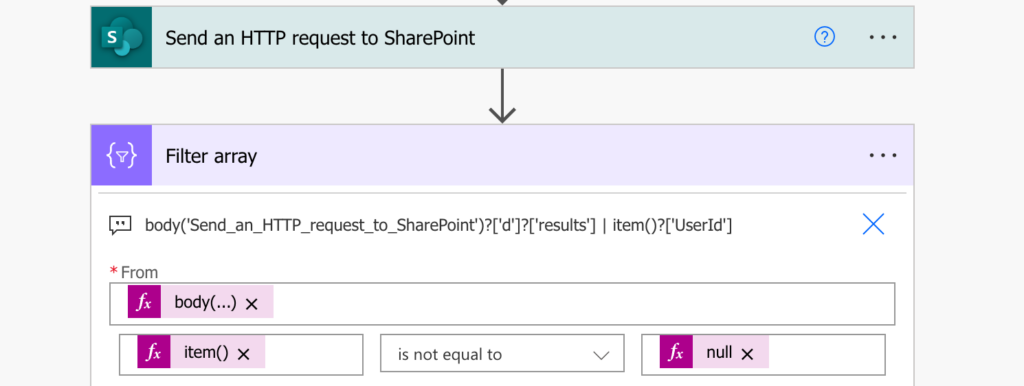
The result will be only users who were added directly into the SharePoint group. Now it’s up to you how to handle them.
Summary
To keep control over sensitive data you should know who can access them. If they’re stored in SharePoint it means knowing who’re the members of related SharePoint group, and Power Automate can help you with that. Get the users in the SharePoint group, filter out the AD groups as they’re often managed, and keep only the members added directly. In an ideal situation it should never find such users.
Excellent explanation. Exactly what I was looking for. Thanks
Can you update this to be able to grab users from multiple groups?
_api/web/siteGroups/getByName(‘[Entity]’)/users
The SharePoint item can have up to two Permission groups on a submission, and we need to notify all the users from both groups. Thank you for your assistance!
Hello Maria,
it can always grab only 1 group, if you have more than 1 group use the request multiple times to get the users from all the groups one by one.
Is it possible to remove owners too with their access for a particular item?
Hello Rakesh,
no, site owners own everything on the SharePoint site, no way to remove them.